Announcing KEY-data support for DNSSEC
We're excited to announce one of our most-requested features is now available: KEY-data support for DNSSEC. We've received a lot of requests about DNSSEC support for certain TLDs that require the KEY-data interface to inform registries whenever the zone is signed.
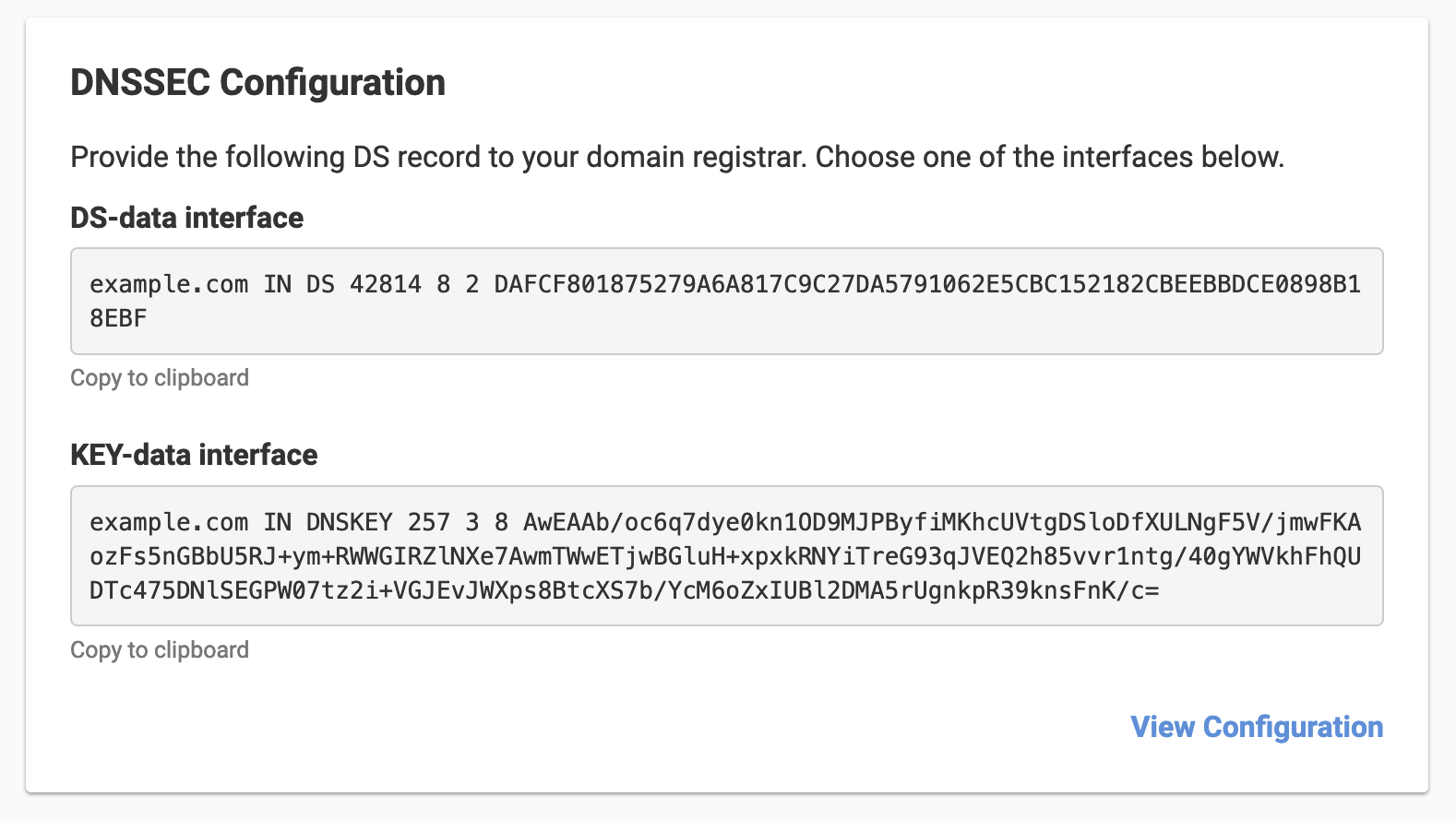
While we previously only supported DS-data interface, you can now use DNSSEC with several TLDs that require the KEY-data interface.
What is DNSSEC?
DNSSEC provides a way to cryptographically build a chain of trust from the root name servers to authoritative name servers. Authenticating resolvers may verify this chain of trust to ensure the DNS results weren't tampered with while in transit.
Whenever a zone is signed, the parent name servers must be notified with the new signing information. There are two formats used to deliver the signing information to registries: DS-data and KEY-data. While most registries require DS-data interface, a small number of registries require the KEY-data interface.
We've enabled DNSSEC for .NL, .BE, and .EU. If you have a TLD not listed here that you'd like to use DNSSEC with, get in touch, and we can enable it for you.
How it works
If your domain is registered with us and delegated through our nameservers, it's a one-click operation. We'll take care of everything for you – including rotating keys automatically every 90 days.
If your domain is registered with us, but you're delegating it through a third party DNS service, there are a couple extra steps. Enter the public key of the key-signing key of your zone signing configuration, and we'll send it to the parent zone. They'll provision the corresponding DS record for your zone.
If your domain is hosted, and you enable DNSSEC on your domain, you'll have access to the configured public key to provide to your registrar.
API Clients with DNSSEC Key Data enabled
- Go API Client
- Ruby API Client
- PHP API Client
- Python API Client
- C# API Client
- Java API Client
- Elixir API Client
- Node JS API Client
And that's a wrap on our release of API clients with DNSSEC Key Data enabled – visit our support documentation to read more about how to enable DNSSEC on your domains.
Want to learn more about DNSSEC? We've got the perfect comic for you at howdnssec.works.
Not using DNSimple yet? Give us a try free for 30 days, or drop us a line to discuss how DNSimple can help with your domain management.
Guillermo Gutiérrez
Father, husband, software developer, amateur cook and baker, coffee enthusiast, maker aficionado, and Oxford comma fan.
We think domain management should be easy.
That's why we continue building DNSimple.

