DNSimple Now Supports Secondary DNS Hosting
We're excited to announce that we have implemented support for inbound zone transfers via AXFR, and you can now add DNSimple as your secondary DNS provider.
For years we've supported zone replication across multiple providers via secondary DNS where DNSimple is the primary DNS provider. This let our users continue taking advantage of our comprehensive API, easy-to-use web interface, powerful DDoS defense, Anycast network, and low response times, and added redundancy in case DNSimple went down.
With DNSimple as a secondary DNS provider, you can leverage all of these things as part of your redundancy strategy – without having to change your primary provider.
Why is secondary DNS important?
Availability is key for all businesses. If your site becomes unavailable, of course you'll lose traffic, but you'll also lose leads and trust. That's why it's important to have a redundancy strategy for your DNS.
Deploying a secondary DNS provider that doesn't share the same infrastructure as your primary provider means if your primary DNS provider goes down, your customers continue to have access to your infrastructure.
If you're not using DNSimple yet, and you're ready to secure your online presence with our secondary DNS, Give us a try free for 30-days. We'll help make sure your site stays up, running, and secure at all times.
How does it work?
Let's go over the basics of primary and secondary DNS (RFC 2182).
-
A primary DNS server hosts and manages the zone files for your domains. Once the primary server has completed applying any updates, it can update any secondary servers and pass along the changes to them.
-
A secondary DNS server stores a copy of the zone file in a read-only mode. This means no changes can be applied via the secondary DNS server to the zone file. The process of copying the zone file from the primary DNS server is called a zone transfer.
Communication between the primary and secondaries is always unidirectional – moving from the primary to the secondary DNS servers. When a zone is updated, it results in an incremental change to the Start of Authority (SOA) serial number. The SOA's serial number is used by the secondary DNS server to determine if the zone is out of sync. The zone update will also result in a NOTIFY message being sent to the secondary DNS server. If they receive the message, they can trigger an AXFR zone transfer (RFC 5936) to sync the zone file. Even if the NOTIFY message never reaches its destination, you can still expect the secondary DNS server to carry out periodic checks on the SOA serial to determine if it needs to initiate a zone transfer to sync the zone file.
Common Secondary DNS configurations
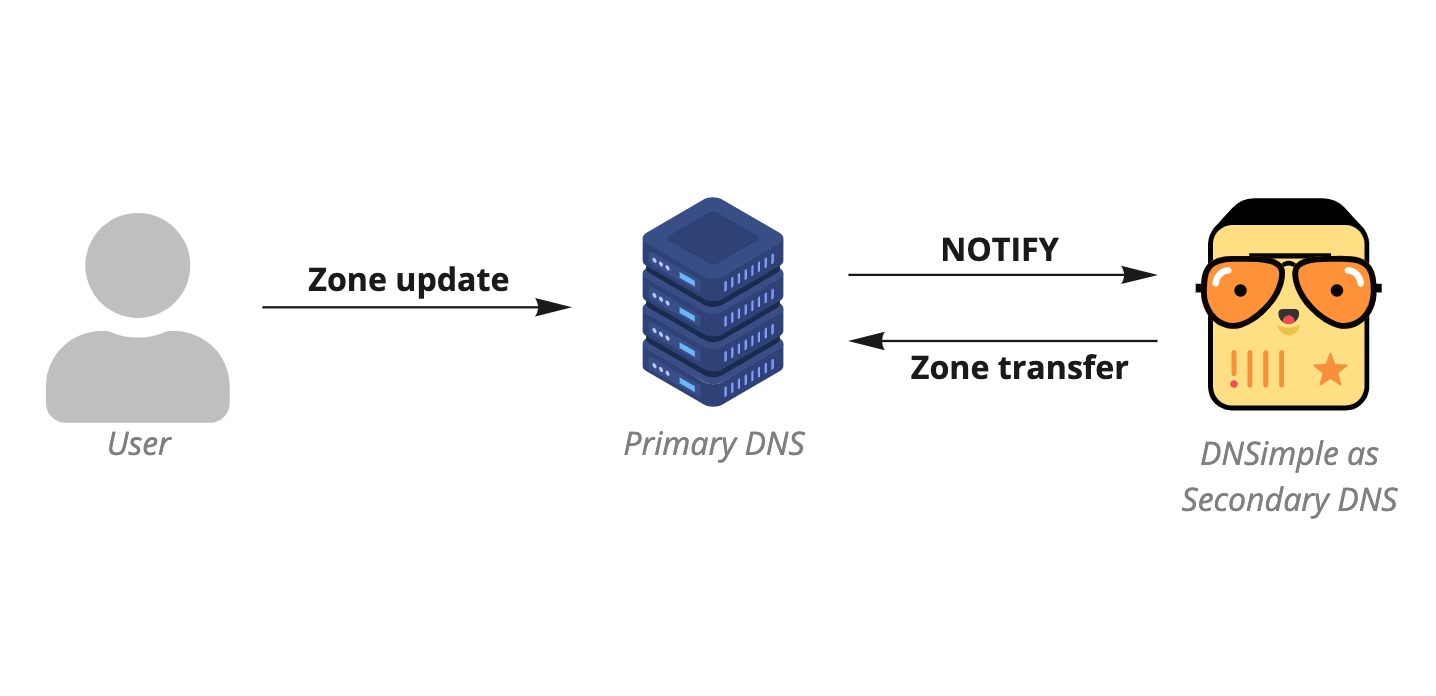
Primary with a secondary DNS provider
In this configuration, DNSimple can be either the primary or secondary DNS provider – for this example, we'll focus on DNSimple as secondary. In this case, the primary DNS provider will be responsible for zone changes, and DNSimple will receive automatic updates whenever a change is made.
The name servers of both the primary DNS provider and DNSimple are set as authoritative for the zone, so both can answer incoming queries.
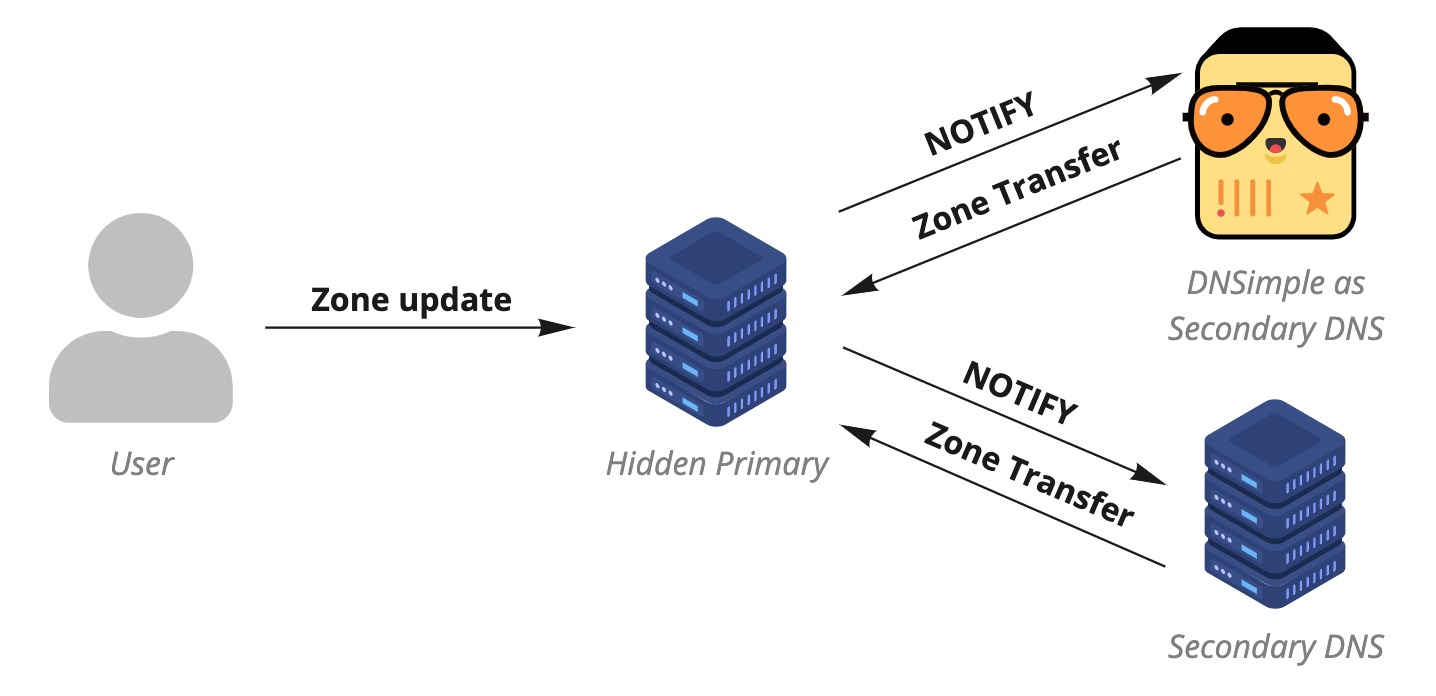
Hidden primary with two secondary DNS providers
In this configuration, you can have the primary DNS server on premise in your private cloud. You'll make zone updates to the primary server, and set two separate DNS providers as secondary servers. Having two secondary providers ensures redundancy in case one of them fails, like in the primary - secondary setup. The name servers for both secondary DNS providers are set as authoritative for the zone (excluding the hidden primary server). The hidden primary server will not receive queries, and the secondaries will be responsible for answering any incoming DNS queries.
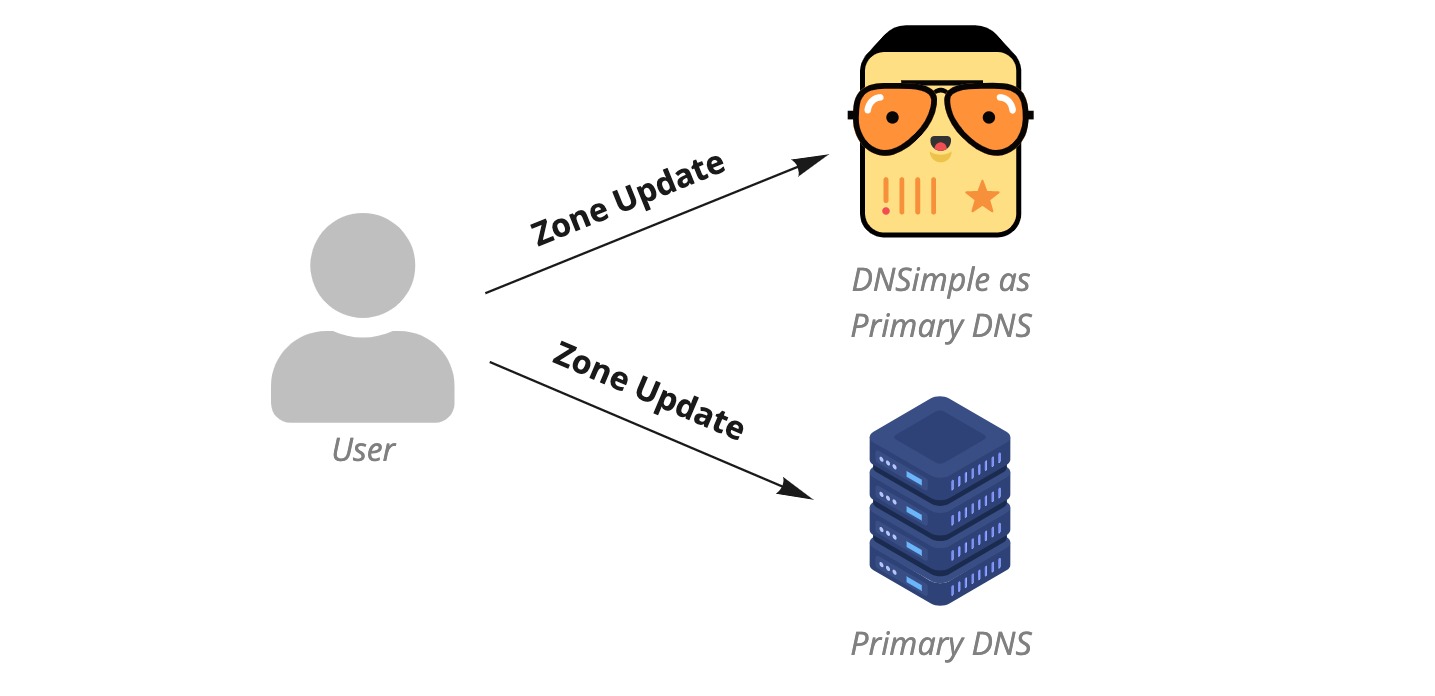
Two primary DNS providers
In this configuration, there's no secondary DNS server relying on a primary to sync the zone file from. Instead, both providers are considered primaries as zone changes are applied to both via their API or manually. The name servers of both providers are set as authoritative for the zone, and both can handle DNS queries.
How do I get started?
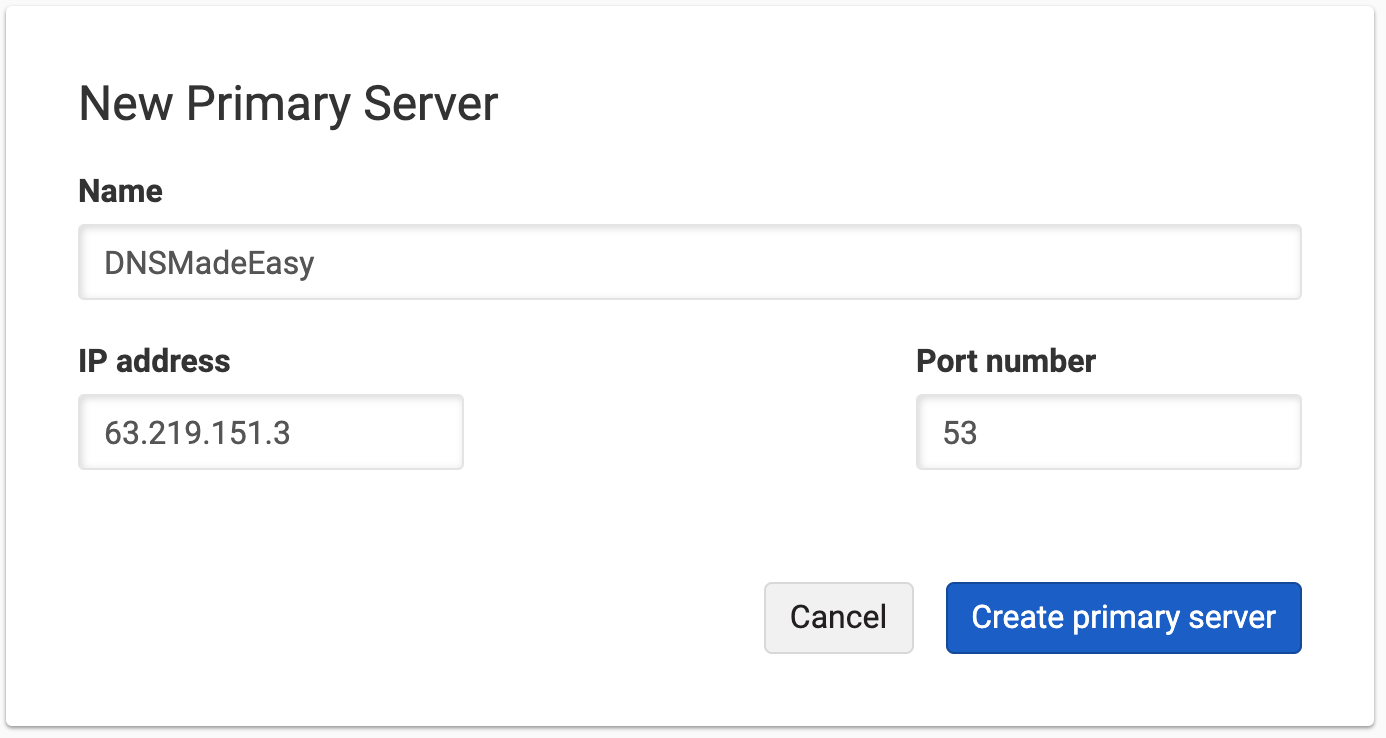
Click on the new "Secondary Zones" tab in your DNSimple dashboard. From there, you'll be able to configure your Secondary Zones and Primary Servers. For help setting up DNSimple as Secondary DNS, follow the instructions in our support article.
Not using DNSimple yet? Give us a try free for 30-days, and experience our robust API and reliable customer-facing code for yourself. Have more questions? Get in touch – we'd love to help.
Ivan Bakalov
Nothing is impossible, it's just a function of effort over time.
We think domain management should be easy.
That's why we continue building DNSimple.