Announcing DNSimple integration with Hashicorp Consul
Automate DNS provisioning – reduce network delays in virtualized & cloud environments
When deploying new projects, or if there's a change in topology, a lot of enterprises still rely on their application operation teams to provision DNS entries. But the lack of automation for DNS provisioning can cause outages and security risks - DNS records are often left behind after a service has been deprovisioned. Manual editing means it can take days if not weeks for a DNS entry to be made, depending on the organization's internal processes.
Network automation lets teams self-service and provision the required DNS records. The process can be as simple as adding the required DNS records in the app's manifest, where they can be tracked and audited. At DNSimple, we strongly believe in automating infrastructure management, and we've made domain and DNS management automation one of our primary goals.
HashiCorp Consul is a service mesh that allows for the discovery of services and securing communications for services within the mesh. Consul has built-in support for discovering services via DNS. But to make it work for public services, it requires provisioning DNS records in public authoritative name servers.
That's where DNSimple's new HashiCorp Consul integration comes in.
When a service is registered or deregistered with Consul, our integration provides the mechanism to provision the requires DNS records in DNSimple's public authoritative name servers, using the DNSimple API.
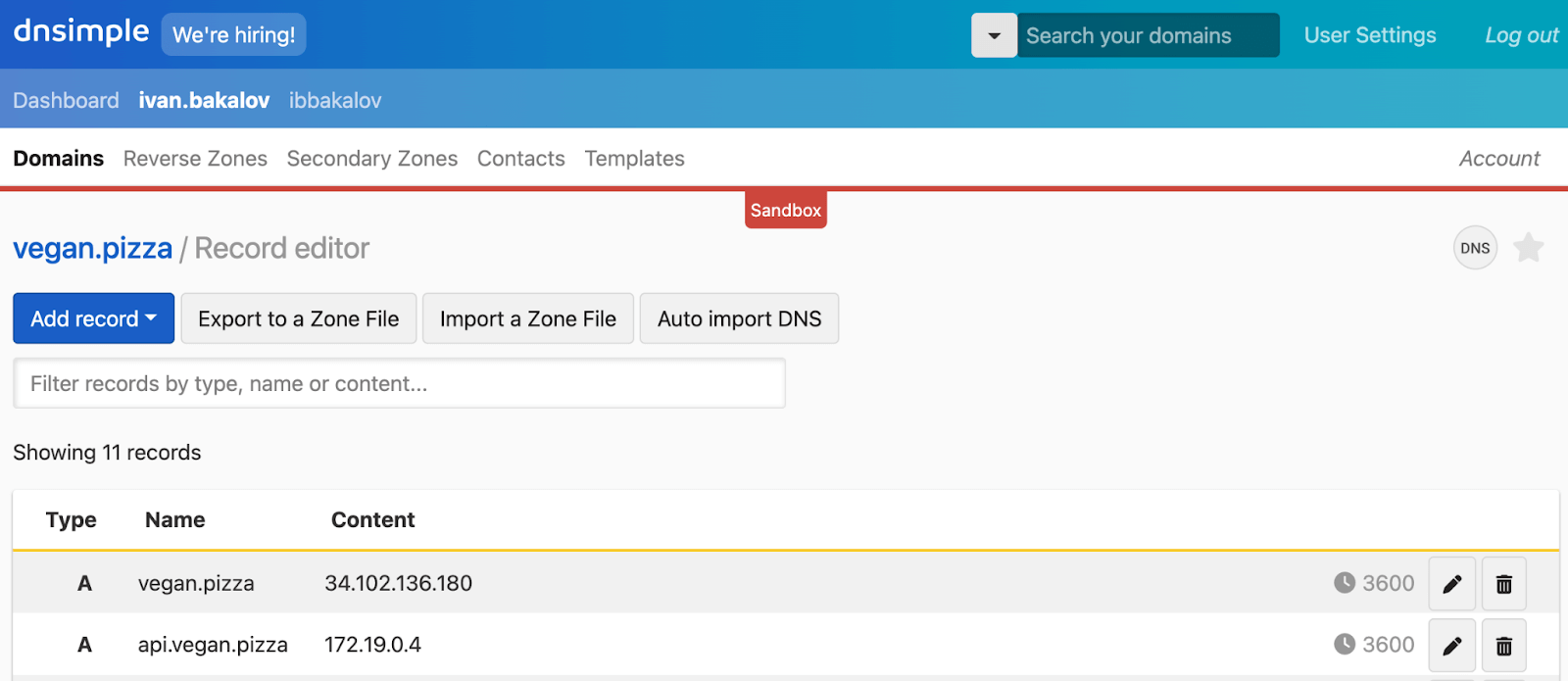
With the DNSimple Network Infrastructure Automation (NIA) Consul integration, operators can automate DNS records provisioning that reacts to changes in the service mesh. When a service is registered or updated, a DNS A record with the service IP address is created or updated in the domain specified by the operator. Similarly, when a service is removed from the mesh, the associated DNS records are also removed from the domain.
Use cases
The most common use case for the DNSimple Consul integration is automatically updating key service DNS records to avoid outages due to DNS misconfiguration, even when the underlying IP address for the service changes. Any public-facing service can immediately benefit from having automated DNS records.
When deploying to a private cloud environment, giving access to the environment via VPN is often not enough. There's no canonical way to resolve access to the services. Having the DNS records created in a public DNS provider like DNSimple, even if the IPs are private users connected to the VPN, can still use the canonical domain names to resolve access to the services. This removes the need to operate a private DNS server.
How does it work?
Consul manages a data plane where it stores service information and configurations. Every time a new service is created, updated, or destroyed with Consul, the network configuration - like the IP address of the underlying VM, container, or bare-metal server where the service runs - is also stored in the data plane. Whenever a CRUD event occurs for a service you're interested in, the Consul server notifies DNSimple.
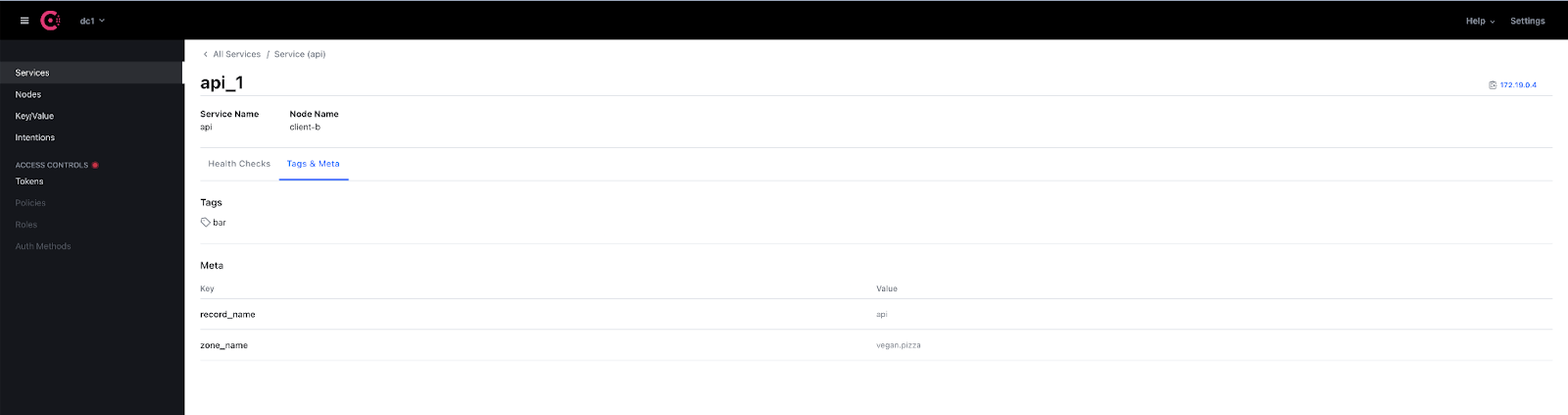
For each Consul service you're subscribed to, an A record will be created in DNSimple with the IP address of each instance where the service is running.
DNSimple API + Consul + Terraform
The DNSimple Consul integration is part of the HashiCorp Consul Network Infrastructure Automation (NIA) program, and is developed using the DNSimple CTS module. It leverages our existing DNSimple Terraform provider to interact with the DNSimple API using our DNSimple Go client.
This is just an example of what you can do with our API. If you want to learn more, visit the DNSimple domain and DNS management API page. If Go isn't your primary choice, we've got several clients for a multitude of programming languages.
Conclusion
The Hashicorp Consul and DNSimple integration automates the deployment of DNS records generated by Consul into your DNSimple account, so your organization can reduce outages and improve security - without needing to wait days or weeks for DNS records to be provisioned.
If you're ready to experience the Hashicorp Consul and DNSimple integration and streamline your network operations, give us a try free for 30 days. If you've got more questions, get in touch – we're always here to help.
Ivan Bakalov
Nothing is impossible, it's just a function of effort over time.
We think domain management should be easy.
That's why we continue building DNSimple.

